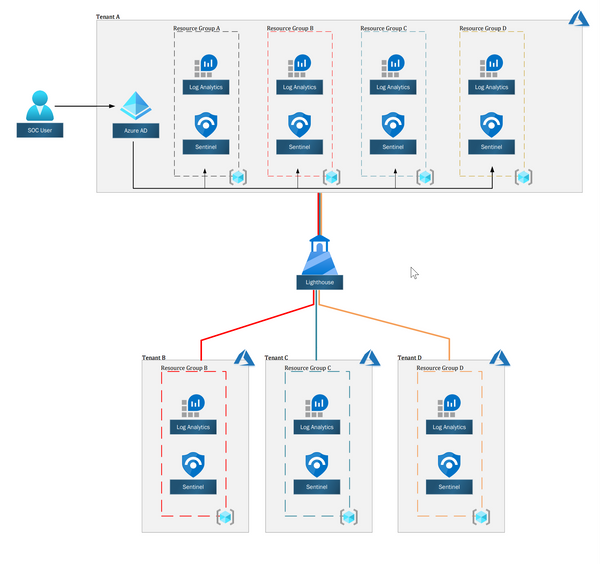
Installing Core Domain Controller in Azure is an easy task, especially if you did it On-premise. Still, there are few things to look out for when doing it in Azure. In this post, I will try to walk you through the required steps for installing Core Domain Controller in Azure.
“Same Same but different”
Smart Thai saying 😂
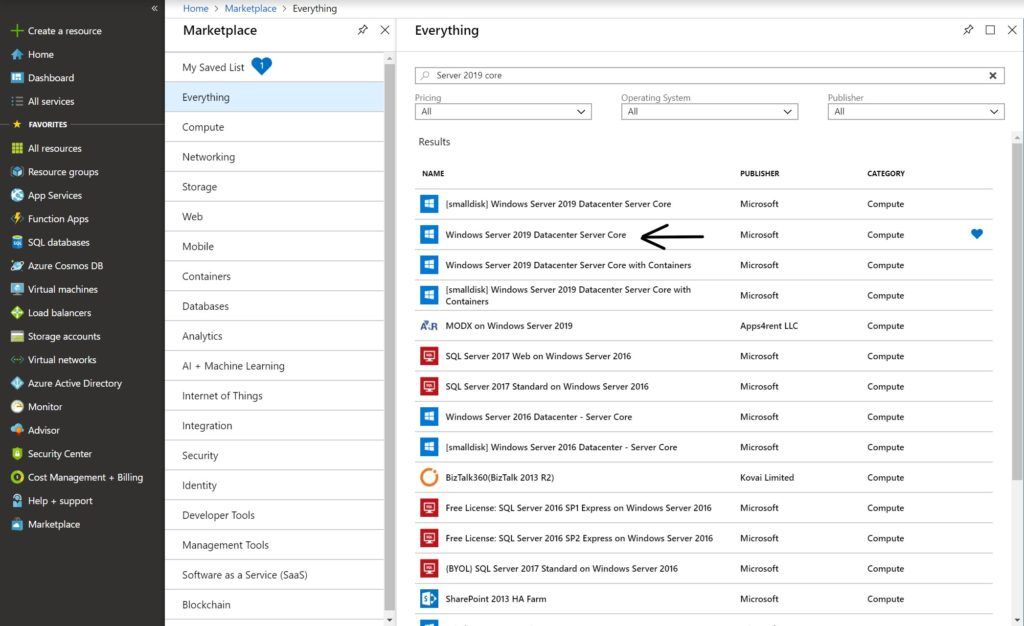
Step 1 – Deploy Virtual Machine
The first thing we need to do is to deploy the virtual machine. In this guide, I will deploy a Windows Server 2019 Core edition. The easiest way is to go to the Marketplace, search for “Windows Server 2019 Core” and deploy it from there.
Step 2 – VM Configuration
When deploying a VM, we need to provide configurations so Azure could build it the way we want and need.
Basics
The first step is to provide basic information for the VM. We will provide the following:
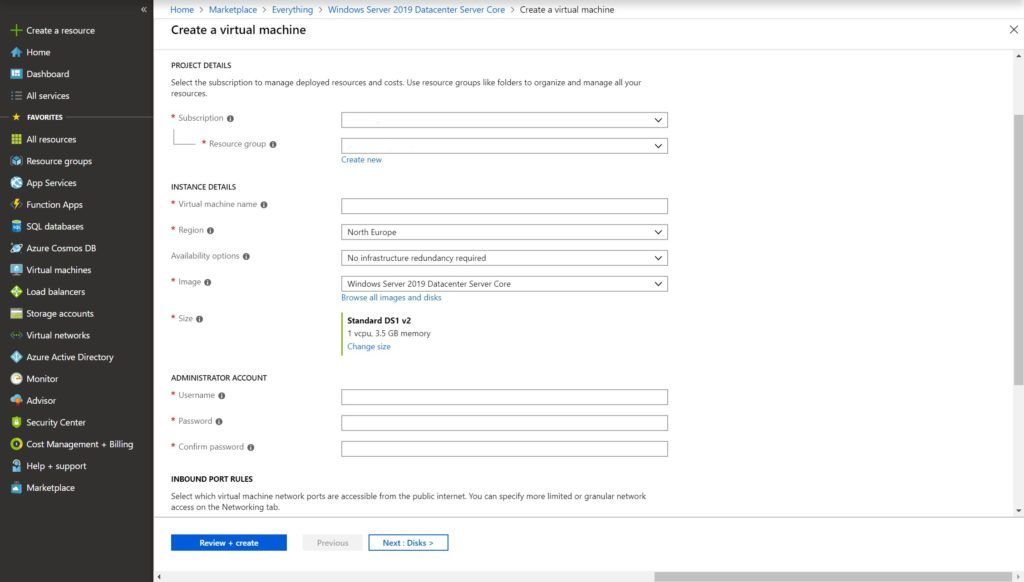
Subscription
Each account must have at least one subscription, all resources in Azure must be part of one subscription so it can be billed.
Resource Group
Resource groups are collections of items that share the same life-cycle permissions and policies. Use it to create a collection of items used for the same purpose, so you can easily manage it.
Virtual Machine Name
The Virtual Machine name.
Region
Azure is multi-regional, it means that they have Datacenters all over the world. Here you specify the Datacenter region you want the VM to be deployed to. Consider the project needs and the effect on the latency. Choose the closest region.
Availability Set
Availability set is a logical grouping capability for isolating VM resources from each other when they’re deployed. This used to provide more reliability VM’s. You can read more about it on Microsoft doc
VM size
Azure provides a wide selection of VM’s sizes. Each size is suited for other needs. Because Azure charges you by your usage, it’s important to choose the right VM size so you won’t pay for resources you don’t use. you can see all the different VM size and purpose.
Administrator Account
The Default Administrator account for the VM. We will use it for the first time we log in to the VM.
Windows License
If you already have a license agreement with Microsoft, you can use it in Azure. This will save you the money for the VM license Microsoft charge in the cloud.
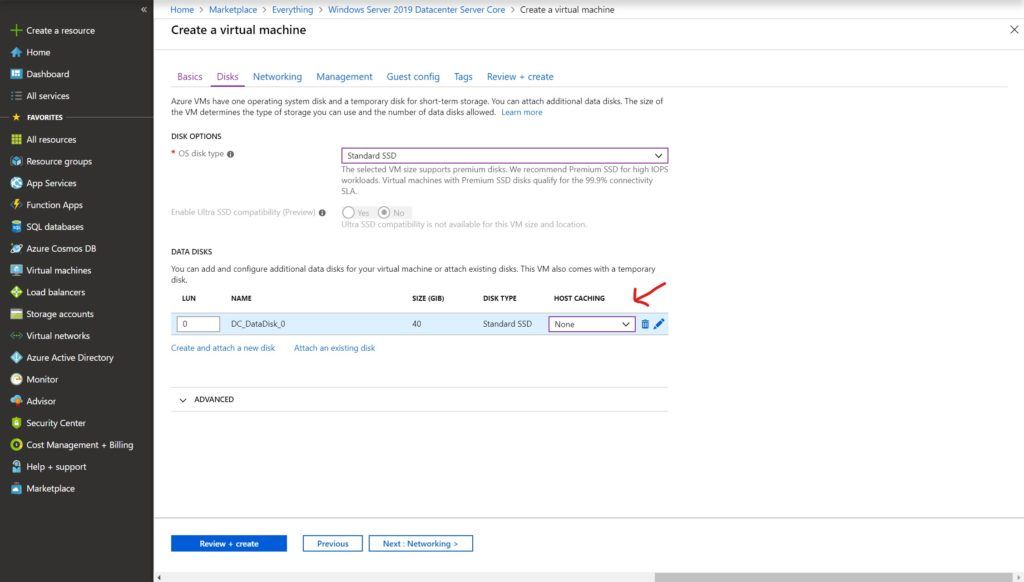
Disks
In this page, we will configure the disks for our VM. Azure provides three tiers of storage: Premium SSD, Standard SSD, and Standard HDD. Each tier has its own price and you should choose what best suit you and your budget.
Azure also use caching by default, and, caching is bad for Active Directory. When we deploy a VM for Domain Controller in Azure, we must add a data disk and set host caching to None. We will put the SYSVOL, NTDS, and Logs on the data drive to avoid replication issues.
Networking
In this step, we will configure the VM networking configuration.
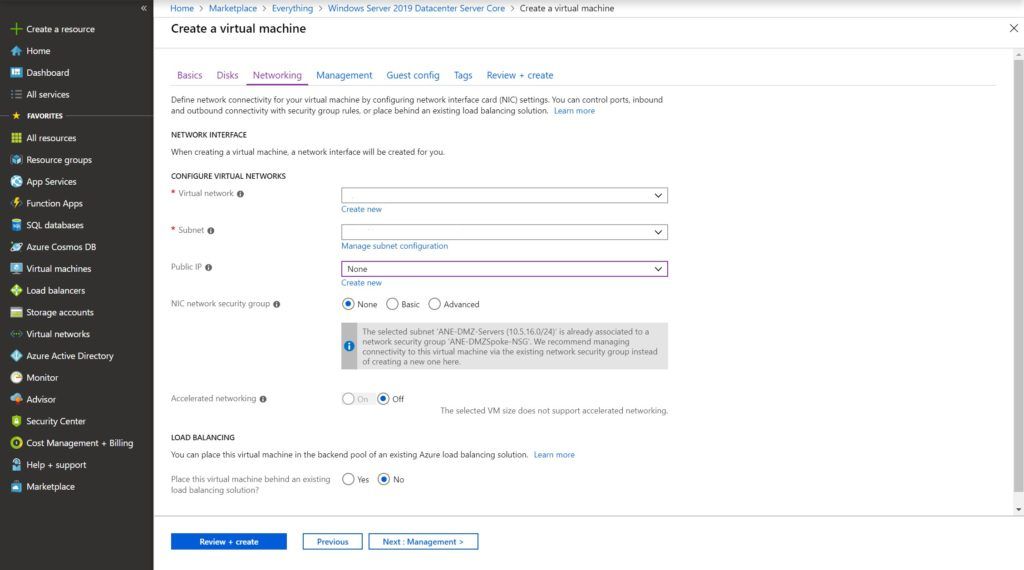
Virtual Network
Azure Virtual Networks or VNets are a representation of our network in the cloud. It is logical isolation dedicated to our subscription.
Subnet
Subnets are the Vlan’s that we know in the On-Premise world, choose or create the one fits your need.
Public IP
Azure can provide Public IP for every VM we create. It assigns the VM a legit public IP that can be accessed from anywhere in the world. It has its costs and not recommended at all for Domain Controllers. Domain Controllers are the most powerful computers in our organization. Exposing them to the internet increase the risk of attacks, potentially leaking your organization users information, escalating permission, or even deleting all your forest.
NIC Network Security Group
Network Security Group or NSG is a simple Firewall for our VM. You can deploy NSG to a VM to micro-control the VM traffic, just the same as VMware NSX. In this guide, we won’t use it.
Review + Create
After configuring the Networking section, we can finally create and deploy the virtual machine.
Step 3 – Post Installation configuration
After Azure finished deploying our Virtual Machine, there are few configurations left to do before we can promote this VM to a Domain Controller.
Configure Static IP
Azure handle networking a little different from what we know. The virtual machines network cards are now individual managed objects in the Azure portal, and not part of the Virtual Machine itself. Domain Controllers should configured with a static IP, which can be achieved by using the GUI or Powershell.
Please note: Changing IP requires a reboot for the VM.
Change IP address using the GUI
To change the IP address using the GUI, we first need to search and navigate to the virtual machine. we can also use the Virtual Machine tab.
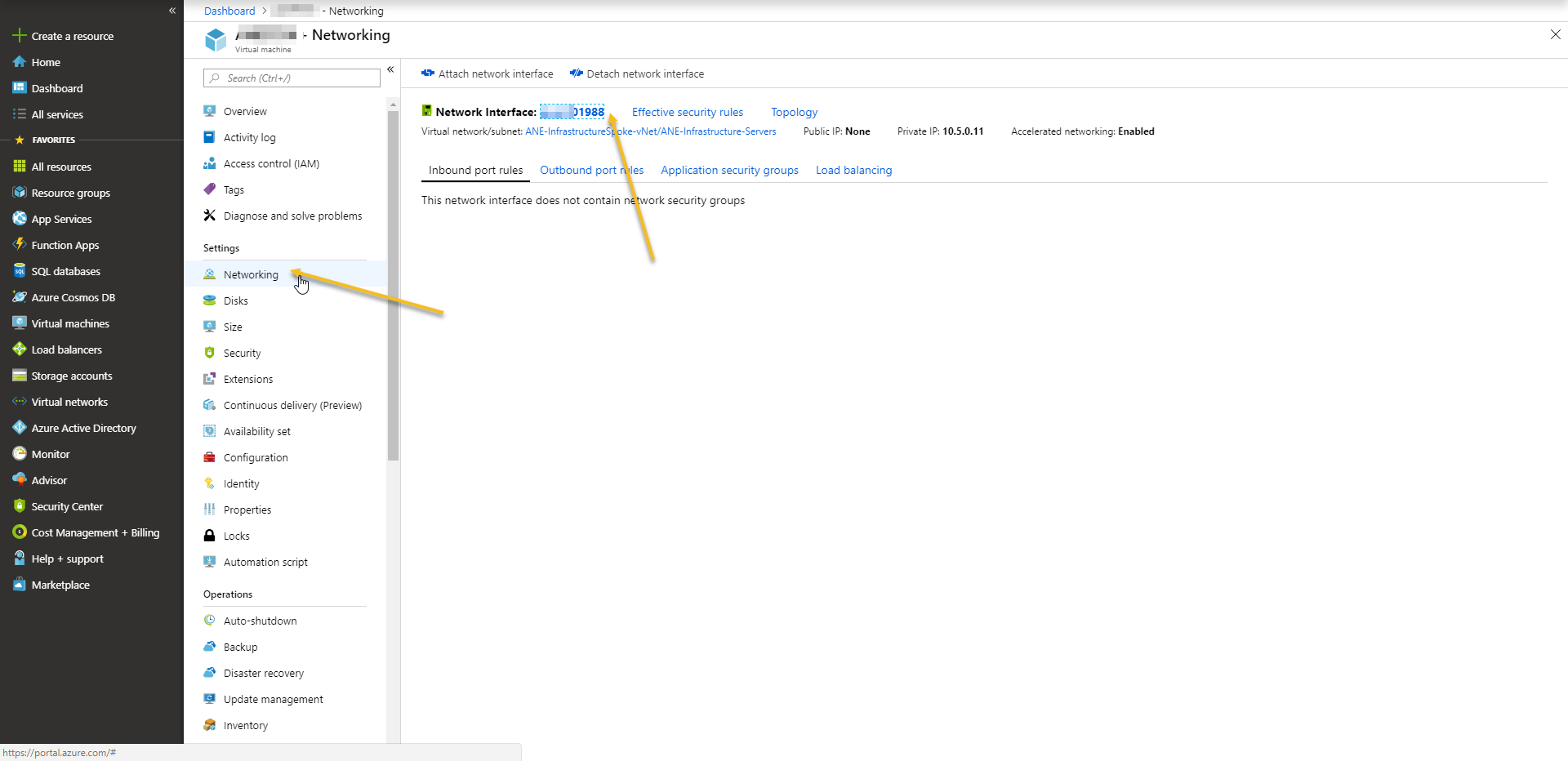
Under ‘Settings’ we can find the ‘Networking’ option. clicking on it will show us the Virtual Machine network card, where we can edit the network card settings.
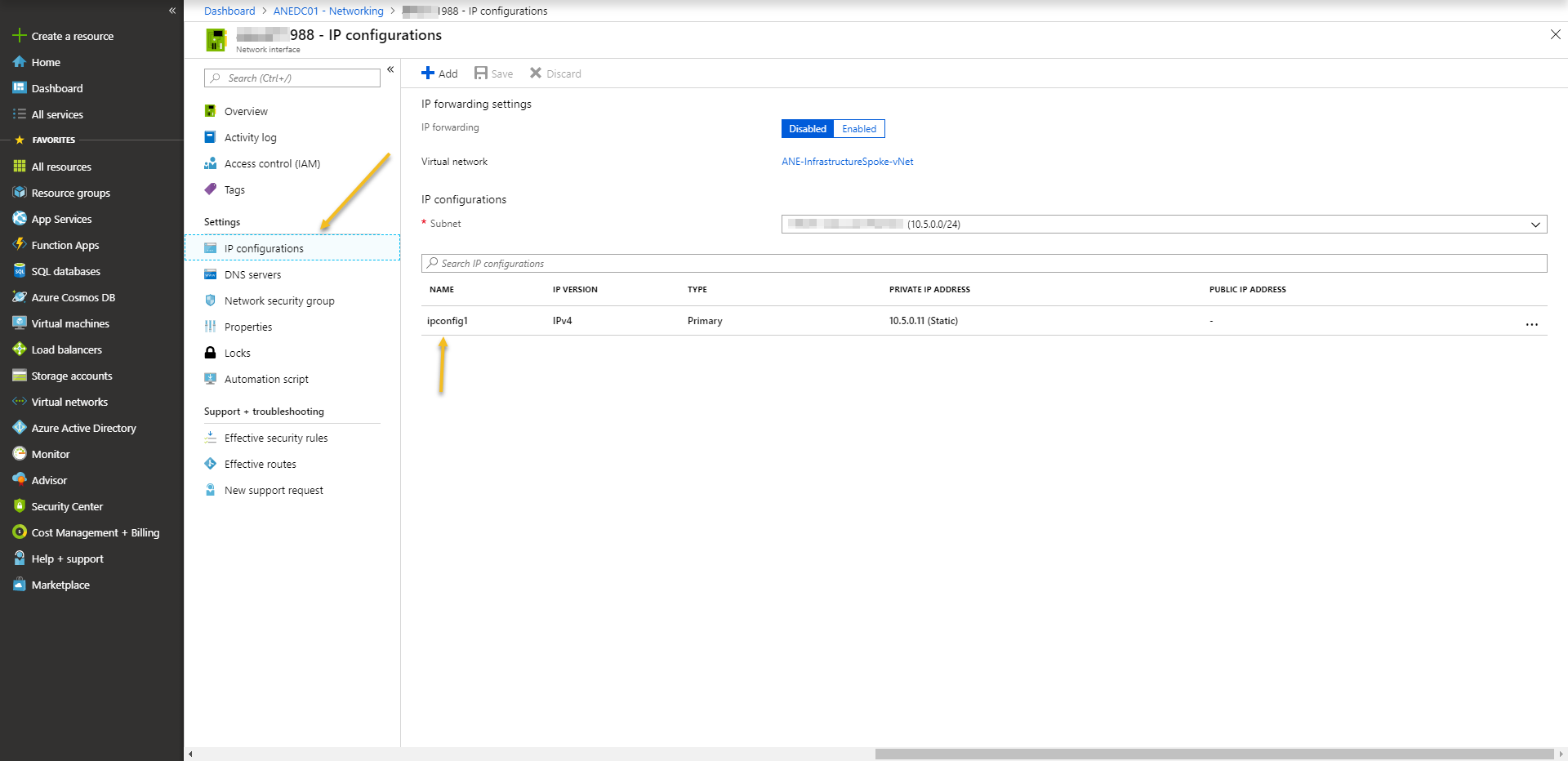
Going to ‘IP Configurations’ and pressing on ipconfig, we can change the settings from dynamic to static.
Change IP address using Powershell
$Nic = Get-AzNetworkInterface -ResourceGroupName "ResourceGroup1" -Name "NetworkInterface1"
$Nic.IpConfigurations[0].PrivateIpAddress = "IP Address"
$Nic.IpConfigurations[0].PrivateIpAllocationMethod = "Static"
Set-AzNetworkInterface -NetworkInterface $NicPlease Note: The first IP address in each subnet is reserved to Azure (used as the default gateway for Azure devices).
Changing DNS Servers
Another configuration we need to set is the DNS servers for the virtual machine. We need to make sure that the VM can reach our domain. Like configuring a static IP, this task also required a reboot and can be performed using GUI and Powershell.
Changing DNS Servers from GUI
Continue with the same NIC configuration, select ‘DNS Servers’.
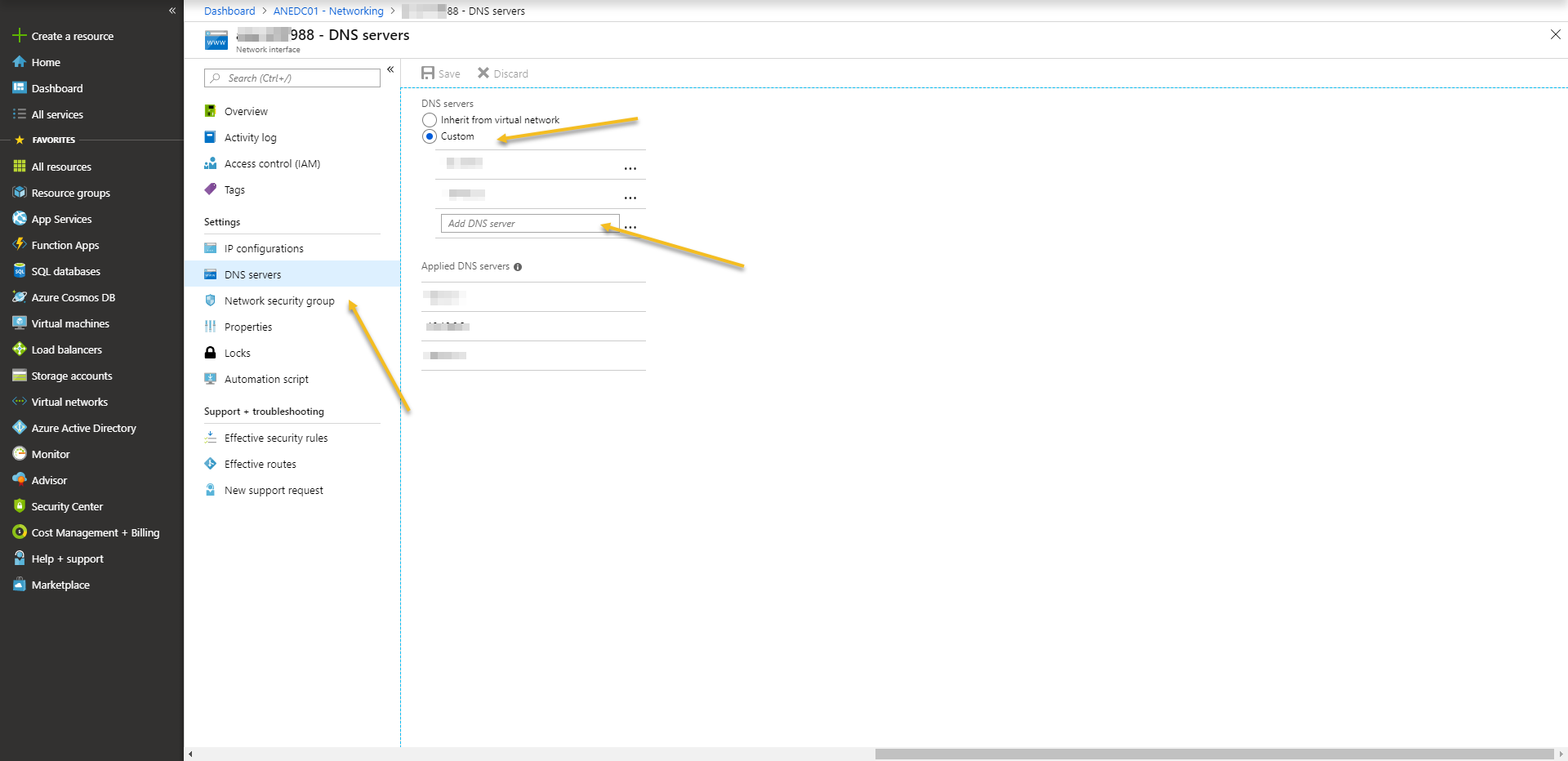
We need to change it from ‘Inherit from virtual network’ to ‘custom’ and type the DNS servers IP address as required.
Changing DNS Servers from Powershell
$nic = Get-AzNetworkInterface -ResourceGroupName "ResourceGroup1" -Name "NetworkInterface1"
$nic.DnsSettings.DnsServers.Add("DNS Server")
$nic.DnsSettings.DnsServers.Add("DNS Server")
$nic | Set-AzNetworkInterfaceDisable Windows Firewall (optional)
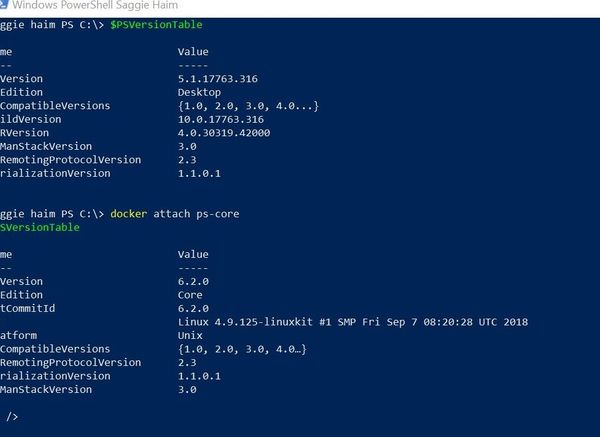
Afterward, we can log in for the first time to the VM. We will start with a reboot if you didn’t reboot yet after changing the IP Address and the DNS servers. After the restart, verify the network configuration.
While Microsoft not recommending to disable the Windows Firewall (A new set of firewall rules are automatically created when promoting a new Domain Controller), not many use it. If we want to disable the Windows Firewall, we can do it using Powershell.
When we first login to a core server, we get a CMD prompt, we can start Powershell by simply typing Powershell. We will then use the Get-NetFirewallProfile and Set-NetFirewallProfile to disable all Firewall profiles:
Get-NetFirewallProfile | Set-NetFirewallProfile -Enabled FalseInitialize and create a partition for the Data disk
When we created the VM, we added a data disk. Azure add the data disk without initializing it. We need to initialize the disk and create a partition before we can continue. To do this we will run the following commands:
Get-Disk | Where-Object Partitionstyle -eq 'raw' | Initialize-Disk -PartitionStyle MBR -PassThru | New-Partition -AssignDriveLetter -UseMaximumSize | Format-Volume -FileSystem NTFS -NewFileSystemLabel "DataDisk" -Confirm:$falseAfter initializing and partitioning the disk, Azure sometimes doesn’t assign a Drive Letter to the new partition. Therefore, it is recommended to verify the drive letter existence and, to do so, run ‘Get-Partition’ cmdlet to get all partitions and their drive letters.
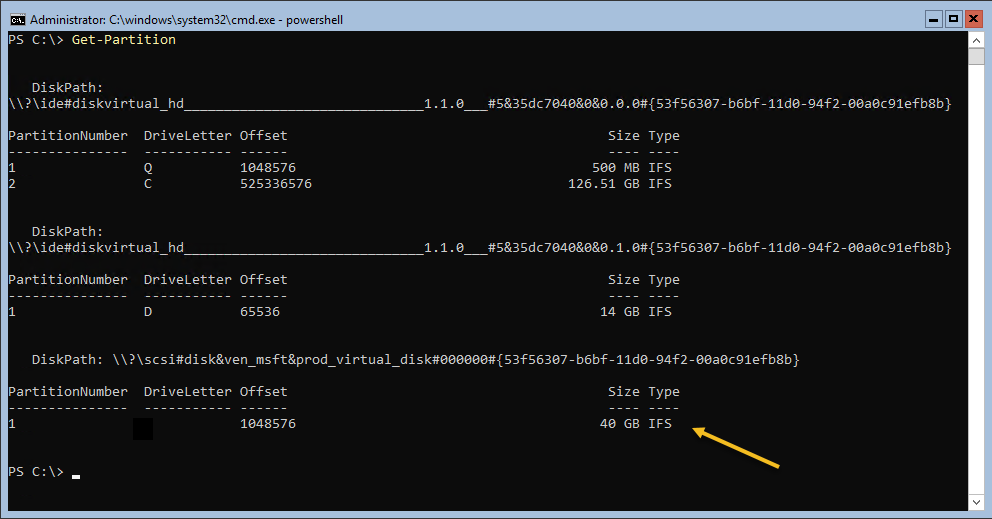
If the partition has no drive letter assigned, we can assign a new drive letter using the Set-Partition cmdlet:
Get-Partition -PartitionNumber 1 | Set-Partition -NewDriveLetter EStep 4 – Install Core Domain Controller in Azure
We made a long way, and we can finally install the Domain Controller. from this point, it’s almost identical to the On-Premise. The only difference is the location of the SYSVOL, NTDS, and the logs path.
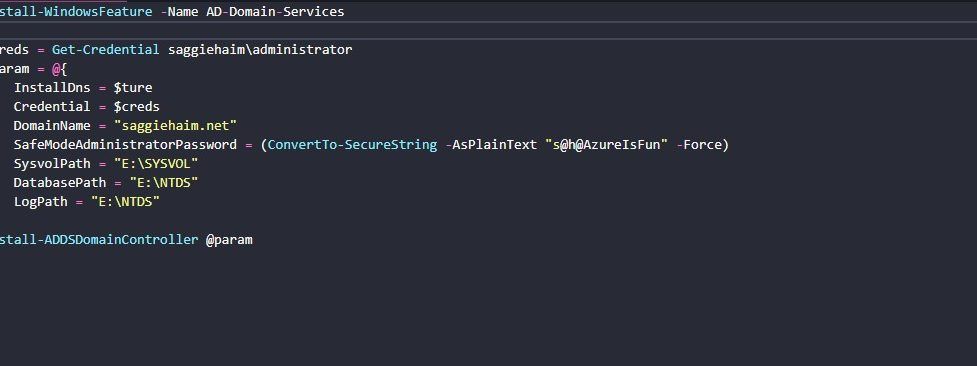
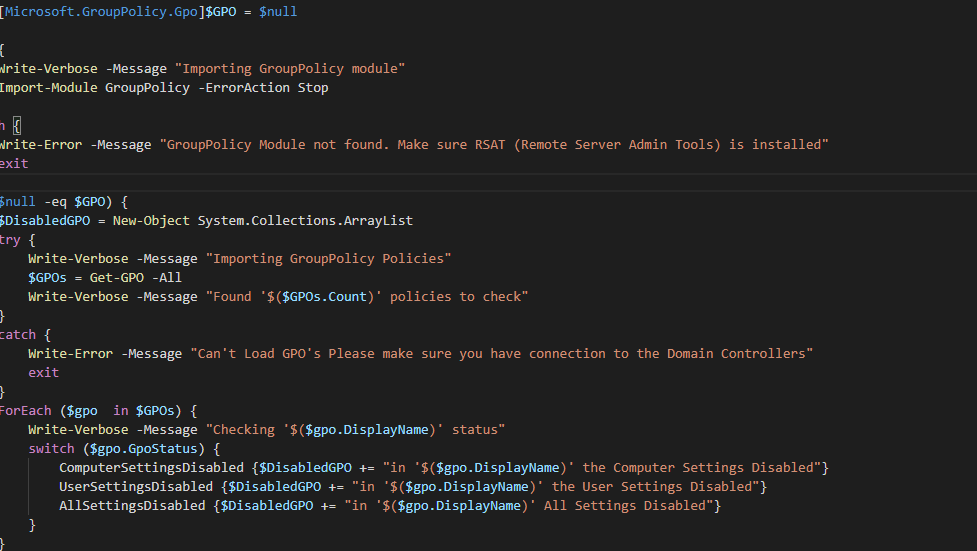
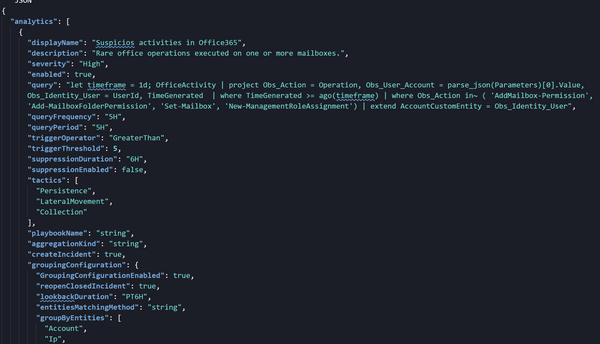
Installing AD domain services feature
First, we need to install the AD-Domain Services:
Install-WindowsFeature -Name AD-Domain-ServicesPromoting the VM to a Domain Controller
Second, we promote the server to an Active Directory Domain Controller. We need to provide the following:
$creds = Get-Credential saggiehaim\administrator
$Param = @{
InstallDns = $ture
Credential = $creds
DomainName = "saggiehaim.net"
SafeModeAdministratorPassword = (ConvertTo-SecureString -AsPlainText "s@h@AzureIsFun" -Force)
SysvolPath = "E:\SYSVOL"
DatabasePath = "E:\NTDS"
LogPath = "E:\NTDS"
}
Install-ADDSDomainController @paramStep 5 – Changing the DNS Servers
Our last step includes changing primary and the secondary DNS servers in the Domain Controller itself. Microsoft best practices say that the primary DNS server should point to another domain controller, This will prevent a delay during a startup DNS request. The secondary server should be the loopback address to delegate the requests if the primary server has an issue. Go back to step 3 if you don’t remember how to make this change.
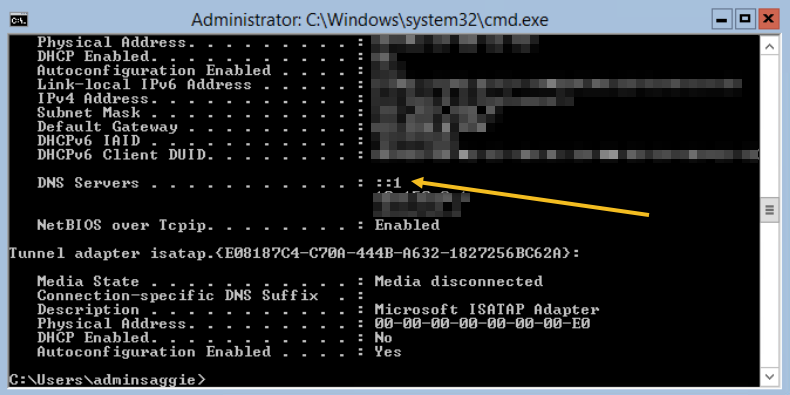
In addition, we need to remove the ::1 IPv6 DNS. By default, when you install a domain controller, it add the IPv6 ::1 as DNS server. It will also point to this address first, which is something we don’t want to happen.
Removing the IPv6 is a very simple task, and we can accomplish it using with the following steps:
first, identify the interface configured with ‘::1’ using the Get-DnsClientServerAddress cmdlet.
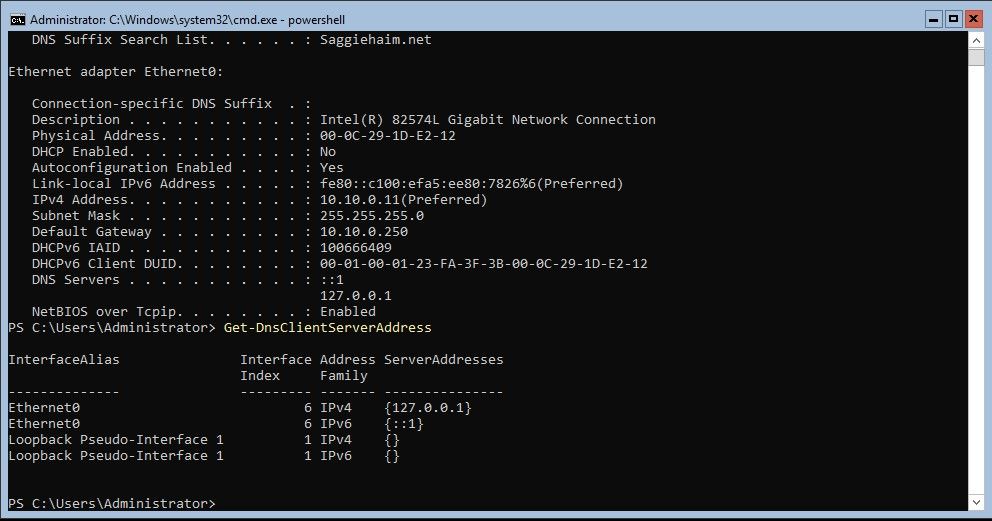
In this example above, we can see that the Interface Index is “6”, so we will run the following cmdlet upon this interface:
Get-DnsClientServerAddress -InterfaceIndex 6 -AddressFamily IPv6 | Set-DnsClientServerAddress -ResetServerAddressesIf no error occurred, the ::1 DNS server will be removed.
Conclusion
In this post, we learned how to install a Core Domain Controller in Azure. Remember to disable Azure disk caching on your AD DS database and SYSVOL by creating additional data disk for AD DS files. Also, Remember to set a static IP for the AD DS, and make sure to protect the AD DS and don’t assign a Public IP. Pay attention to the DNS Servers in each step, and make sure to monitor any replication issues with your new AD DS. Good luck!